Why Digital Verification Services Will Redefine How Businesses Consume Government Data.
Clara Benson
•
4 Mar 2026
•
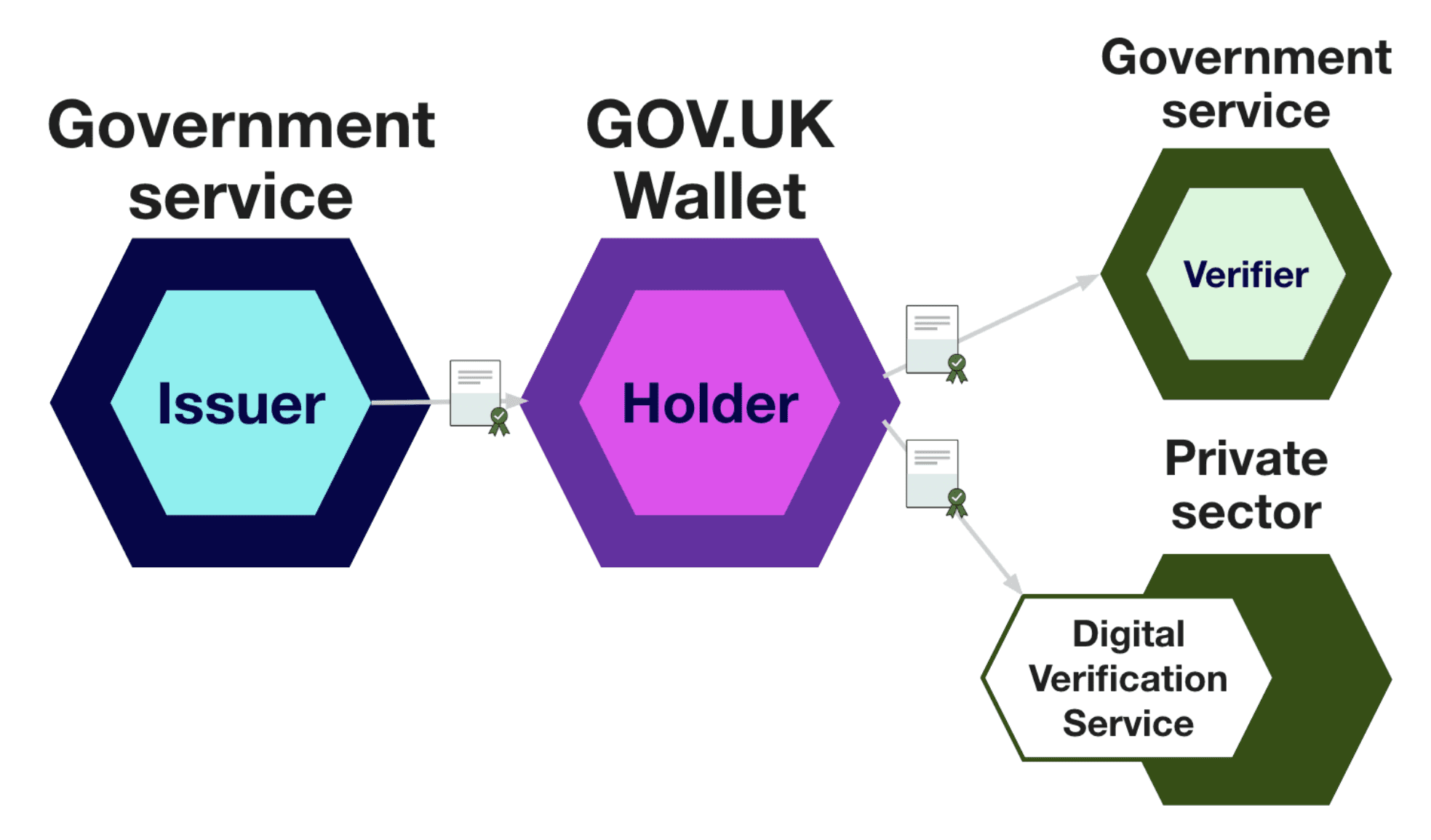
The publication of the Consuming and verifying credentials in GOV.UK Wallet - Wallet data flow model is not simply a technical update. It signals a structural shift in how government held data will be consumed by the private sector.
For decades, verification has revolved around documents. Scans, PDFs, manual checks, portal uploads. The process has been human led, asynchronous, and operationally heavy.
The wallet model changes that.
Government issues a credential.
The individual holds it.
A business requests a specific attribute.
A certified Digital Verification Service provider orchestrates the secure, consented exchange.
Verification moves from document submission to structured data flow.
That distinction is fundamental.
From Documents to Machine Verifiable Data
Under the GOV.UK Wallet architecture, verification is not about collecting evidence. It is about requesting precisely what is needed, obtaining explicit consent, and receiving a cryptographically verifiable response.
The DVS provider is the operational bridge. It enforces policy, manages consent, ensures minimal disclosure, and translates trust into a machine readable response that can be embedded directly into business workflows.
This is not middleware in the traditional sense. It is trust infrastructure.
Without orchestration, wallets remain containers. With orchestration, they become usable at scale.
Why Orchestration Is the Strategic Layer
Issuers create credentials. Wallets store them. But businesses cannot realistically integrate directly with every issuing authority, schema, or policy regime.
The orchestration layer provides governance enforcement, interoperability across credential types, contextual policy application, structured yes or no or attribute responses, and operational integration into live systems.
It is where regulatory logic meets commercial workflow.
That is why powerful orchestration services will become the primary way businesses serve and consume government data.
A Broader Structural Shift
This direction is not unique to the UK. Across Europe under eIDAS 2.0 and in other advanced digital economies, the same architecture is emerging. Issuers. Holders. Verifiers. Orchestrators.
As government issued credentials become standardised, the competitive question shifts from whether you can verify to how efficiently you can embed verification into your operations.
The answer lies in orchestration.
The Competitive Divide
Established organisations that adopt structured orchestration services early will gain more than incremental efficiency. They will reduce operational cost, minimise manual compliance overhead, and future proof their integration with government issued digital credentials.
The advantage is structural.
Processes that currently depend on document handling, human review, and fragmented system checks can be redesigned around verifiable, consented data flows. That shift delivers measurable savings in time, risk management, and operational resilience.
At the same time, challenger businesses are not constrained by legacy systems. They can design services natively around wallets and orchestration layers, embedding verification directly into onboarding, eligibility checks, and regulated workflows from day one.
This creates a clear divergence.
Incumbents who modernise intelligently will operate leaner and more securely. New entrants who build around orchestration from the outset will redefine expectations.
Either way, structured digital verification mediated through certified orchestration services will move from the edge of business processes to the centre of operational design.
From Theory to Operational Reality
In a recent workshop with a fintech client, we mapped a long compliance heavy onboarding process. Multiple document uploads. Manual reviews. Re requests for missing information. Delays driven by verification friction.
When re-framed through an orchestration model, the journey collapsed into three discrete interactions with a Xertilox wallet.
A structured request for a specific credential or attribute. Explicit consent from the customer. A cryptographically verifiable response returned instantly.
No PDFs. No re keying. No duplication.
What had been a complex financial process became a controlled, flexible, user friendly data exchange.
This is not cosmetic digital transformation. It is the redesign of regulated operations around machine verifiable trust.
The Strategic Imperative
As wallet ecosystems mature, businesses will not compete on access to government data. They will compete on how intelligently they orchestrate it.
Those who treat orchestration as core infrastructure will reduce operational cost, improve regulatory assurance, accelerate onboarding, strengthen customer experience, and increase resilience.
Those who delay will find themselves maintaining document based systems in a data flow world.
If you are looking to streamline your onboarding or operational processes and move from document handling to structured, verifiable data flows, get in touch at info@xertilox.com.

